Table of Contents
The Evolution of Document Verification in India’s Digital Age
Document verification in India has undergone a significant transformation. The old ways of handling physical paperwork and manual checks are rapidly giving way to digital solutions. This shift is driven by the need for secure and efficient identity verification in India’s growing digital economy. It’s a fundamental change in how trust is established across various sectors. Think about the difference between physically submitting loan documents and securely uploading them online. This illustrates the move towards increased security and fraud prevention.
Key Drivers of Change
Several factors contribute to this evolution. The rise of online transactions, especially in e-commerce and financial services, demands faster and more reliable document verification. Government programs like Aadhaar, a biometric system covering over 1.3 billion people, have established a foundation for digital verification. Aadhaar makes accessing services and benefits easier while improving security. Also, increasingly complex fraud requires advanced technologies to confirm document authenticity.
The Indian identity verification market is experiencing substantial growth. Reaching $451.1 million in 2024, it’s expected to hit $1,719.7 million by 2033, with a 16% CAGR. This demonstrates the critical need for secure digital processes. This is influenced by government regulations like KYC (Know Your Customer) and AML (Anti-Money Laundering) compliance, as well as growing cyber threats. More statistics are available here: https://www.imarcgroup.com/india-identity-verification-market. These regulations shape the market and influence the technology used for document verification.
Impact Across Sectors
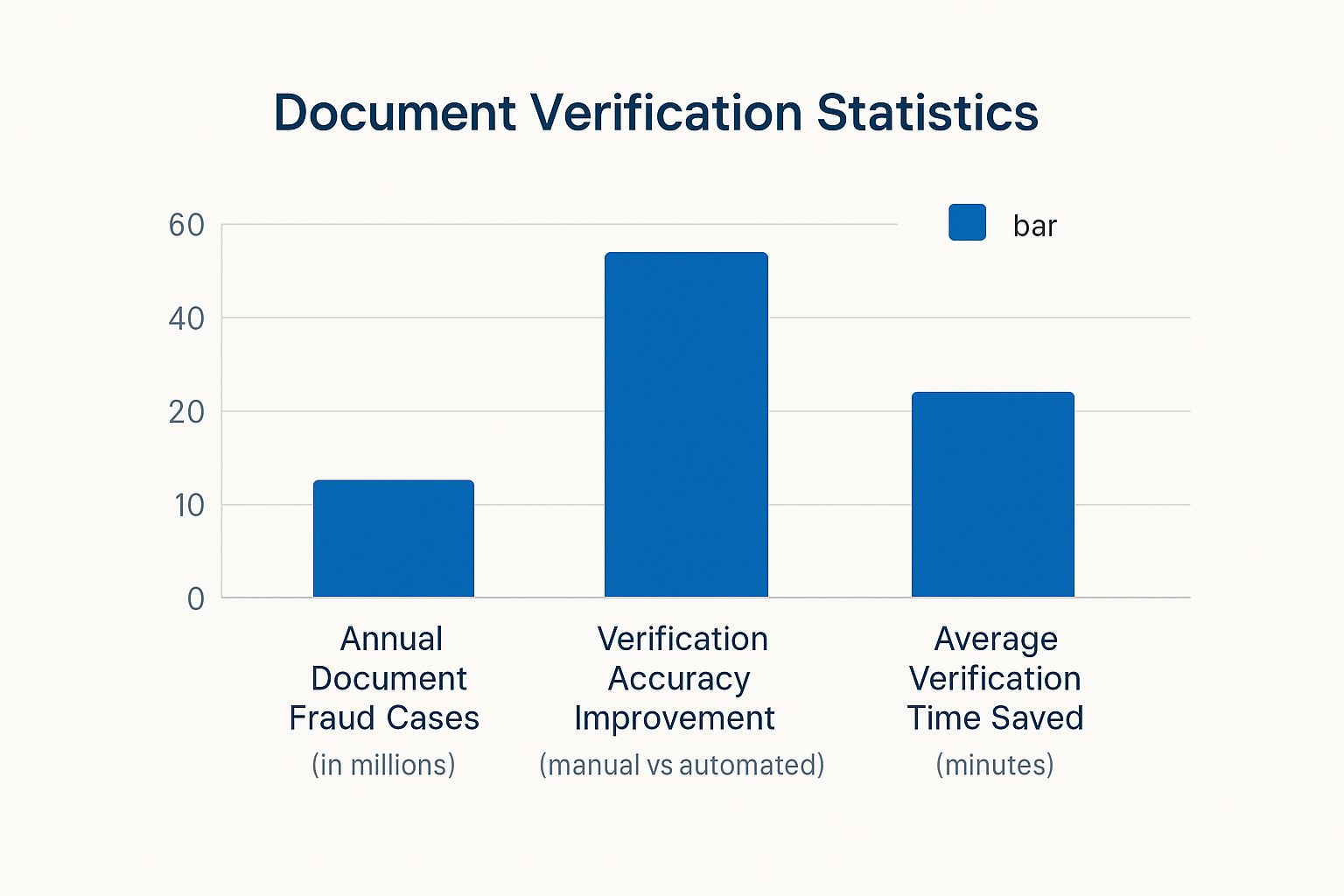
The data chart below visualizes the projected growth of the Indian document verification market, showing its rapid acceleration between 2025 and 2033.
[Insert Bar Chart Infographic Here]
The chart highlights the dramatic projected growth in market value, reflecting the increasing importance of robust document verification systems across industries. This growth is a result of the rise in digital transactions combined with increasingly sophisticated fraud techniques. This growth emphasizes the importance of document verification for trust and security. As the market expands, the demand for adaptable verification solutions to address these challenges also grows. The trends suggest a need to invest in secure processes to mitigate risks and ensure transaction integrity. This trend will likely continue as businesses look to streamline operations and build trust in digital interactions.
To understand the growth trajectory, let’s look at the projected figures:
The following table, “Growth of Document Verification Market in India”, shows the progression and projected growth of India’s document verification market over time.
| Year | Market Value (in millions USD) | Growth Drivers |
|---|---|---|
| 2024 | 451.1 | Increased online transactions, Aadhaar implementation, rising fraud |
| 2033 | 1,719.7 | KYC/AML compliance, cyber threats, digital economy expansion |
This table summarizes the market’s rapid growth from $451.1 million in 2024 to a projected $1,719.7 million by 2033. Key drivers include the growth of online transactions, government initiatives like Aadhaar, and the increasing need for robust security measures to combat fraud and cyber threats. This underscores the growing importance of document verification in India’s evolving digital landscape.
Critical Documents and Their Verification Requirements

Document verification involves more than just glancing at IDs. It demands a thorough understanding of the various document types, their hierarchy within the system, and the built-in security features. This process is essential for building and maintaining trust and security across various sectors. This nuanced understanding is even more vital given the regional differences in documentation practices across India.
Primary vs. Supporting Documents
Effective verification hinges on understanding the difference between primary and supporting documents. A primary document, like an Aadhaar card, PAN card, or passport, serves as the foundation of identity verification. These documents are designed with robust security features that make them challenging to counterfeit.
Supporting documents, such as utility bills or bank statements, play a complementary role. They add another layer of information, corroborating the details presented in the primary documents. For instance, a bank statement can verify an individual’s stated address. This distinction between primary and supporting documentation is crucial for a truly comprehensive verification process.
Sector-Specific Verification
The strictness of document verification procedures varies considerably across different industries. Banking, given its inherent vulnerability to financial fraud, demands rigorous and thorough document checks – much more so than, say, retail.
This means financial institutions typically verify multiple documents and often employ advanced techniques to ensure authenticity. In contrast, a simple retail purchase might only require a single photo ID. Understanding these sector-specific nuances is essential for businesses to implement appropriate and efficient verification processes.
Recognizing Security Features
Successful document verification also relies on the ability to identify subtle security elements embedded within documents. These include holographic features, microprinting, and watermarks, which are frequently overlooked by those attempting fraud.
Take the Ashoka emblem on a PAN card, for example. It possesses specific characteristics that can be verified. The quality of the paper and the printing technique itself can also be indicators of authenticity. Learning to spot these features enables verification professionals to quickly differentiate between genuine and counterfeit documents. This expertise is crucial for effective fraud prevention and maintaining regulatory compliance. You might be interested in: How to master identity verification.
Regional Variations and Compliance
India’s diverse regional landscape adds a layer of complexity to verification. Different states may issue documents with varying formats and security features. Furthermore, all verification processes must adhere to evolving regulatory frameworks, including the Information Technology Act, the Prevention of Money Laundering Act, and the Digital Personal Data Protection Act.
This requires ongoing training and adaptation for verification professionals to remain up-to-date on the latest security measures and compliance requirements. This adaptability is key to ensuring consistent and legally sound verification practices across all regions. Understanding these regional variations and regulatory updates is critical for a robust and legally compliant verification process.
To illustrate the key documents and their verification aspects, the table below offers a helpful comparison:
Essential Documents for Verification Across Sectors
A comparison of primary identity documents accepted across various sectors in India and their key verification features.
| Document Type | Acceptability Score | Key Security Features | Primary Use Cases |
|---|---|---|---|
| Aadhaar Card | 9 | Biometric data, Unique Identification Number, Demographic information | Identity verification, Address proof, KYC compliance |
| PAN Card | 8 | Holographic image, Permanent Account Number, Photograph | Tax compliance, Financial transactions, Identity verification |
| Passport | 10 | Biometric data, Digital signature, Machine-readable zone | International travel, Identity verification, Address proof |
| Voter ID Card | 7 | Photograph, Electoral roll details, Unique identification number | Voting, Identity verification, Address proof |
| Driving License | 6 | Photograph, License number, Issue and expiry dates | Driving authorization, Age proof, Identity verification |
The table above highlights the importance of understanding the various security features and common use cases of each document type. This knowledge allows for a more targeted and effective verification process, depending on the specific sector and its requirements. By understanding the relative strengths and applications of each document, businesses can tailor their verification procedures to best mitigate risk and ensure compliance.
Technology Transforming Document Verification Landscape

Technology has dramatically changed how we verify documents. The once tedious manual process is becoming automated and far more accurate, thanks to advancements in fields like Artificial Intelligence (AI) and Machine Learning (ML). This shift has significant consequences for Indian businesses across various sectors.
AI and Machine Learning: The New Verification Standard
AI and ML algorithms can now analyze numerous security features on a document simultaneously. This drastically reduces verification times and improves accuracy. For instance, these technologies can quickly spot inconsistencies in fonts, microprinting, or holographic elements that a human eye might miss. This rapid analysis helps businesses onboard customers quickly and efficiently.
Moreover, AI-powered systems continuously learn and improve. As they process more documents, they become even better at detecting sophisticated forgeries. This constant learning ensures verification processes stay ahead of evolving fraud tactics. You might be interested in: How to master API integrations.
OCR Technology: Extracting Information with Precision
Optical Character Recognition (OCR) technology is another significant advancement in document verification. OCR allows systems to extract information from scanned documents or images with incredible accuracy. This eliminates manual data entry, reducing errors and significantly accelerating the verification process. OCR also enables systems to quickly search and compare data across numerous documents, simplifying compliance checks and investigations.
Biometric Verification: Seamless and Secure
Biometric verification adds an extra layer of security and ease of use. Using unique biological identifiers like fingerprints or facial recognition allows businesses to verify a person’s identity with high certainty. This method not only strengthens security but also creates a smoother user experience, especially for mobile transactions.
Real-World Implementations and Challenges
India’s identity verification infrastructure is experiencing a major transformation. This is largely driven by regulations mandating secure digital onboarding. The market is projected to grow at a 16.7% CAGR between 2025 and 2033, highlighting the increasing importance of document verification in sectors like fintech and healthcare. Learn more about India’s identity verification market here: India Identity Verification Market Size, Share, Trends Report.
While these technologies offer substantial benefits, implementing them presents challenges. Integrating new systems with existing infrastructure can be complex, and maintaining data privacy and security is paramount. However, numerous organizations in India have successfully navigated these challenges, demonstrating the advantages of these technologies. These organizations are now benefiting from faster processing times, decreased fraud, and greater customer satisfaction.
Navigating the Regulatory Maze of Document Verification
Document verification is more than just confirming a document’s existence. It involves understanding the intricate regulatory landscape governing these processes. In India, this means navigating key legislation like the Information Technology Act, the Prevention of Money Laundering Act (PMLA), and the Digital Personal Data Protection Act (DPPA). These laws establish the foundation for secure and legitimate document verification practices.
Understanding Key Legislation
The Information Technology Act governs the handling and legal recognition of electronic documents. The PMLA, focused on preventing financial crimes, mandates specific verification procedures for financial institutions. The DPPA regulates data processing, emphasizing consent and data security within verification procedures. These regulations are the cornerstone of compliant verification practices.
Practical Verification Protocols
Putting these legal requirements into practical verification protocols can be complex. For instance, the DPPA requires explicit consent for collecting and processing personal data. This means communicating transparently with users about how their data is used during verification. The PMLA also mandates strict record-keeping for financial transactions, influencing how verification data is stored and audited. These examples highlight the practical implications of regulatory compliance.
Staying Ahead of Regulatory Change
Regulations are always evolving. Proactive organizations prioritize compliance. They consult with legal experts, track legislative updates, and adapt their verification systems accordingly. This proactive stance ensures ongoing compliance while minimizing operational disruptions. Read also: How to master compliance.
Sector-Specific Requirements
Different sectors have unique compliance needs. The Reserve Bank of India (RBI) has specific guidelines for financial institutions, outlining how customer verification of document should be conducted. The Securities and Exchange Board of India (SEBI) also mandates certain verification procedures for investment platforms. Understanding the science behind file compression is important for optimizing file management. For more information on file size reduction, see this resource: reduce file size. Navigating these sector-specific requirements is crucial for developing robust and compliant verification systems.
Balancing Compliance and Efficiency
While compliance is paramount, organizations must also maintain operational efficiency. This requires designing verification processes that are both secure and user-friendly. Implementing automated systems for initial document checks can significantly reduce processing time. However, incorporating human review at critical points safeguards against sophisticated fraud. This balance is essential for achieving both security and operational efficiency. Finding the right balance between compliance and efficiency is a continuous challenge in India’s dynamic regulatory environment. Successfully navigating these complexities is key to building trust, mitigating risk, and thriving.
Building Bulletproof Document Verification Systems
Building a reliable document verification system is more than just picking the right software. It’s a strategic balancing act between robust security and a smooth, user-friendly experience. This guide offers a practical approach to creating such a system, focusing on multi-layered processes, smart document capture techniques, data privacy, and thorough staff training.
Multi-Layered Verification: Combining Automation and Human Review
Effective verification systems often use a multi-layered approach, combining the speed of automated checks with human judgment. The first layer might use automated Optical Character Recognition (OCR) technology to extract data and run basic checks. For example, an automated system can quickly confirm if the information on a PAN card matches the applicant’s provided information.
AI-powered algorithms can analyze security features like microprinting and holograms. However, for high-stakes verification, human review is essential. Trained professionals can spot subtle discrepancies or forgeries that automated systems might miss. This blend of automation and human oversight creates a robust and reliable process.
Optimizing Document Capture: Lighting and Resolution
The quality of document images directly impacts verification accuracy. Just like a clear photo is crucial for an Aadhaar card, capturing crisp images is paramount in document verification. This means using proper lighting and ensuring images have enough resolution to capture fine details.
Providing clear instructions to users on how to capture and upload documents makes a big difference. Advising users to avoid shadows and glare when taking photos, for example, can dramatically improve image clarity and make automated data extraction more efficient. This focus on image quality improves both automated and manual checks.
Data Privacy and Secure Storage: Protecting Sensitive Information
Protecting user data is paramount. Verification systems must adhere to strict data privacy standards, such as the Digital Personal Data Protection Act. Secure storage protocols, including encryption and access controls, are essential. Think of it like a bank vault designed to safeguard valuable assets. Your system should employ equally robust security measures to prevent unauthorized access and data breaches.
Staff Training: The Human Element of Security
Even with the most advanced technology, the human element remains vital. Training staff on the latest verification techniques, security features, and regulatory requirements is key. Regular training sessions and updates help staff stay ahead of evolving fraud tactics.
This ongoing education ensures your verification system remains effective against increasingly sophisticated fraud attempts. Just like regular software updates are crucial for maintaining computer security and performance, regular training keeps your team equipped to handle the latest challenges in document verification. This investment in staff training strengthens the entire system.
Overcoming Real-World Verification Challenges

Document verification presents unique challenges that demand flexible solutions. This section examines common obstacles organizations encounter and offers practical strategies to address them. A successful document verification system relies on solid product management principles. For a deeper dive into these processes, check out this helpful resource on Product Management Processes.
Handling Poor Document Quality
Low-quality documents, especially from remote areas, pose a significant challenge. Blurry photos, obscured information, or damaged documents hinder automated processing and often necessitate manual review.
One solution is providing users with clear instructions and visual guides for capturing document photos. Tips on lighting and holding the document steady can dramatically improve image quality. Furthermore, incorporating AI-powered image enhancement tools can help clarify blurred or partially obscured details.
Managing Inconsistencies Across State-Issued Documents
Variations in document formats across different Indian states add complexity to the verification process. The design and security features of a driver’s license, for instance, can differ significantly between states.
Training verification systems on a diverse dataset of documents from all Indian states is crucial. This allows the system to recognize regional variations and accurately extract information. A human review step for potentially inconsistent documents ensures high accuracy.
Overcoming Connectivity Issues
Real-time verification relies on stable internet connectivity, which can be problematic in remote areas. Connectivity issues can cause delays and frustration for users and businesses.
One approach is developing offline verification capabilities. This allows for basic checks even without internet access, with the full verification completed upon connectivity restoration. This offline functionality ensures essential services remain uninterrupted.
Adapting to India’s Multilingual Environment
India’s linguistic diversity adds another layer of complexity. Documents issued in various languages can be difficult for a single system to process accurately.
The solution is integrating multilingual support into the verification system. Using OCR software capable of recognizing multiple languages ensures accurate data extraction regardless of the document’s language. This promotes inclusivity and efficiency.
Addressing Document Fraud
The increasing sophistication of document fraud demands continuous adaptation. Fraudsters constantly develop new methods to create counterfeit documents that can bypass basic security checks.
Verification systems must incorporate advanced security measures, such as AI-powered fraud detection algorithms. These algorithms analyze patterns and anomalies indicative of forgery, including manipulated images or digitally altered documents. Regularly updating these systems is crucial for maintaining effective security.
Contingency Planning for System Outages
Even robust systems can experience outages. Contingency plans for system downtime are essential, including backup servers, redundant systems, and manual verification procedures.
These backup plans ensure business continuity and minimize disruption. Just as a backup power generator is essential during a power outage, contingency plans for system outages are vital for uninterrupted verification services.
Ready to experience seamless and secure document verification? Visit SpringVerify today to explore our comprehensive solutions.






