Table of Contents
India’s Data Breach Landscape: Understanding the Threat
India’s increasing reliance on digital technologies has, unfortunately, made it a significant target for cybercriminals. Businesses across various sectors, from banking and healthcare to technology, are facing a growing risk of data breaches. This increasing threat has serious consequences for organizations of all sizes, impacting not only their financial stability but also their carefully built reputations. Understanding the particular challenges within India is essential for developing effective safeguards.
The Rising Tide of Data Breaches in India
The sheer amount of data created and stored digitally in India makes it a tempting target. This digital expansion, while beneficial for the economy, has also broadened the opportunities for malicious actors. In recent years, India has seen a substantial increase in data breaches, with 5.3 million accounts compromised in 2023 alone. This places India fifth globally in terms of breached accounts, highlighting its attractiveness as a target for cyberattacks. The financial consequences are significant, with the average cost of a data breach reaching $2.18 million in 2023. Phishing and compromised credentials remain the most common attack methods, underscoring the need for strong security measures and user education. The Indian government’s initiatives to strengthen cybersecurity, such as the Digital Personal Data Protection Act 2023, aim to tackle these weaknesses and improve data protection. For more detailed statistics, check out the Corbado Blog on Data Breaches in India.
Sector-Specific Vulnerabilities
Different industries in India face unique cybersecurity hurdles. For instance, the healthcare sector, which handles sensitive patient information, is frequently targeted by ransomware attacks. The financial services industry, with its high volume of transactions, is particularly vulnerable to fraud and phishing attacks. This sector-specific targeting necessitates customized security approaches to address the unique vulnerabilities of each industry.
Emerging Attack Patterns
Cybercriminals are continuously refining their tactics. They increasingly employ advanced techniques like social engineering, malware, and ransomware to exploit weaknesses. Businesses in India must stay alert and adapt their security strategies to counteract these evolving threats. This requires a proactive, rather than a reactive, security posture, including regular vulnerability assessments and penetration testing.
The Cost of Inaction
Disregarding the threat of data breaches can have serious repercussions for organizations in India. Besides the immediate financial costs associated with incident response and data recovery, there are long-term consequences to consider. Reputational damage, erosion of customer trust, and regulatory penalties can severely harm a business. Proactive investment in preventing data breaches is not simply a security precaution; it’s a vital business strategy. This involves a multi-faceted approach combining technical safeguards with employee training and robust security governance.
Vulnerability Mapping: Where Indian Organizations Fall Short
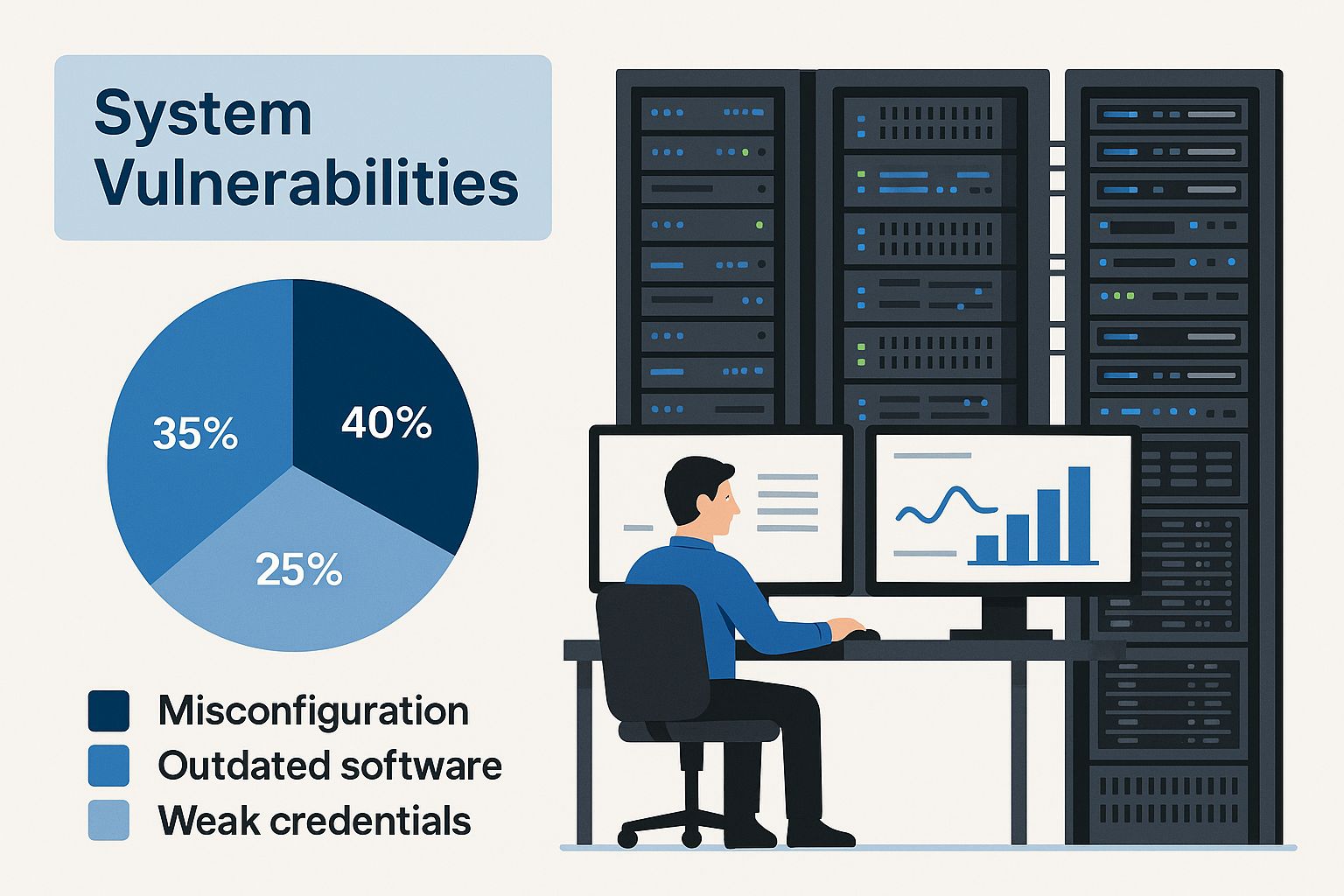
The infographic above illustrates a typical server room, highlighting potential vulnerabilities within this seemingly secure environment. This emphasizes the importance of a comprehensive approach to data breach prevention, moving beyond physical security to encompass technical, procedural, and cultural aspects.
Technical Vulnerabilities: Outdated Systems and Software
Many Indian organizations rely on legacy systems and outdated software. This creates vulnerabilities, as these technologies often lack crucial security patches, making them prime targets for cybercriminals. Insufficient investment in modern security tools like Nessus further compounds the problem. Analyzing recent breaches, such as the incident at T-Mobile, provides valuable insight into the current threat landscape. Regular security audits and proactive system upgrades are crucial for strengthening technical defenses.
Procedural Vulnerabilities: Lack of Robust Security Policies
Beyond technical weaknesses, inadequate security procedures significantly contribute to vulnerabilities. A lack of clear security policies, insufficient employee training, and weak access controls can create opportunities for breaches. Many organizations still lack robust incident response plans, leaving them ill-equipped to handle a security event. This absence of defined procedures amplifies the impact of breaches and prolongs recovery.
Cultural Vulnerabilities: A Mindset Shift
Often overlooked, the cultural aspect of security is vital. A lack of awareness regarding data security within some Indian organizations can lead to negligent practices, such as password sharing or clicking phishing links. Security awareness training tailored to the Indian context is crucial to foster a culture of shared responsibility for data protection.
The following table presents a breakdown of common security vulnerabilities affecting Indian businesses. It highlights the prevalence of these weaknesses, their associated risk levels, and the primary sectors affected.
Top Vulnerabilities in Indian Organizations
| Vulnerability Type | Prevalence (%) | Risk Level | Primary Sectors Affected |
|---|---|---|---|
| Outdated Software | 60 | High | IT, Finance, Healthcare |
| Weak Access Controls | 50 | Medium | All Sectors |
| Lack of Security Awareness Training | 70 | High | All Sectors |
| Insufficient Incident Response Planning | 40 | Medium | IT, Finance |
| Legacy Systems | 45 | High | Government, Manufacturing |
This table illustrates the high prevalence of preventable vulnerabilities like outdated software and lack of security awareness. These weaknesses pose a significant risk across various sectors, emphasizing the need for immediate action.
The Indian cybersecurity landscape faces evolving threats and improving defenses. 369.01 million malware detections across 8.44 million endpoints in 2024, averaging 702 detections per minute, highlight the constant vigilance required. While the drop in incidents from 10,500 in 2023 to 7,770 in 2024 is positive, the projection that 59% of Indian organizations anticipate a breach in 2025 demonstrates the ongoing challenge. More detailed statistics can be found here. Addressing these vulnerabilities demands a holistic approach encompassing technical upgrades, procedural improvements, and a cultural shift towards prioritizing security.
Building Your Breach Prevention Framework That Works

Building a strong data breach prevention framework requires a strategic approach. It needs to address the specific issues facing businesses in India. This means developing a resilient security structure based on global best practices adapted to the local context, not just general security advice.
Understanding the Indian Context
Effective breach prevention in India means understanding the unique aspects of the business environment. This includes the existing technical infrastructure, regulations, and cultural factors. Many Indian organizations use a mix of old and new systems, creating distinct security challenges. India’s evolving regulations, such as the Digital Personal Data Protection Act, also demand a compliance-focused security strategy.
Discussions with Chief Information Security Officers (CISOs) at leading Indian companies show that successful prevention strategies prioritize understanding the context. This means recognizing the specific threats Indian businesses face and adapting security measures accordingly. For instance, many organizations face growing threats from social engineering and phishing attacks that exploit cultural sensitivities and the country’s linguistic diversity.
Key Components of an Effective Framework
A data breach prevention framework needs several key elements. These include threat assessment, security governance, and incident response planning. These components must work together to create a strong defense.
- Threat Assessment: Regularly assess the threats specific to your industry and organization. This means identifying how attacks might happen, understanding the attackers’ motivations, and evaluating the potential damage of a breach.
- Security Governance: Establish clear security policies, procedures, and roles. This ensures everyone in the organization understands their security responsibilities and that proper controls are in place to reduce risks.
- Incident Response: A detailed incident response plan is essential. This plan should outline the steps to take if a breach occurs, including communication protocols, containment strategies, and how to recover.
Balancing Security and Business Enablement
A good prevention strategy balances security with business needs. Security measures shouldn’t slow down productivity or innovation. Instead, they should be seamlessly integrated into business processes. This requires security teams and business stakeholders to work closely together, ensuring security aligns with business goals. During 2024, India saw a significant rise in cyber threats, especially in telecommunications, finance, and healthcare. The Indian Cyber Crime Coordination Centre reported cyber fraud losses of ₹11,333 crore in just the first nine months of 2024. Projections indicate these losses could reach ₹1.2 lakh crore in 2025, almost 0.7% of India’s GDP. Read more about India’s cybersecurity incidents and the financial impact of data breaches. This highlights the financial impact of data breaches and the need for a comprehensive prevention approach. Such an approach should include technology upgrades, employee training, and strong incident response strategies.
Securing Executive Buy-In
Getting leadership support for security initiatives is critical. Clearly explain the risks and potential costs of data breaches to executives. Making a strong business case for security investments, showing the potential return on investment (ROI) through reduced risk and a better reputation, can help secure resources and support. Good communication and demonstrating how security supports business goals are vital for gaining executive buy-in. This ensures that security becomes a strategic priority for the organization.
Technical Safeguards That Actually Prevent Breaches
Building a strong breach prevention framework is a crucial first step. But it’s equally important to reinforce your defenses with effective technical safeguards. These act as the first line of defense against ever-evolving cyber threats. This section examines security technologies offering the best value, specifically for organizations in India, considering the specific obstacles they encounter.
Prioritizing Security Investments for Maximum Impact
Effective breach prevention isn’t about buying the priciest tools. It’s about strategically deploying the right combination of technologies. This means identifying your organization’s vulnerabilities. For instance, if your company relies heavily on cloud applications, robust access management and data encryption are crucial. If you handle sensitive personal data, investing in strong Data Loss Prevention (DLP) mechanisms is essential for compliance and reputation management.
Essential Technical Controls for Indian Organizations
Several technical controls have a proven track record of preventing data breaches in India.
- Encryption: Encrypting sensitive data, both while it’s being transmitted and when it’s stored, renders it unusable to attackers even if a breach occurs. Think of it as a secure vault for your most valuable information.
- Access Management: Implementing robust access controls, such as Multi-Factor Authentication (MFA) and Role-Based Access Control (RBAC), significantly restricts access to sensitive systems and data. This principle of least privilege limits the damage from compromised credentials.
- Network Segmentation: Dividing your network into smaller, isolated sections restricts the spread of attackers. If one segment is compromised, the others remain protected, containing the damage. It’s like the compartments of a ship; if one floods, the whole ship doesn’t sink.
- Threat Detection: Investing in advanced threat detection solutions, such as Intrusion Detection/Prevention Systems (IDS/IPS) and Security Information and Event Management (SIEM) platforms, allows you to identify and react to malicious activity immediately. These tools act as your security radar, alerting you to dangers before they escalate.
Implementing Security in the Indian Context
Implementing these controls requires understanding the specific hurdles within the Indian business environment. This includes selecting solutions compatible with your existing infrastructure and adhering to local regulations. Explore our guide on API Integrations for seamless data transfer and system compatibility.
Evaluating and Selecting Technologies
When selecting security technologies, prioritize proven effectiveness over vendor hype. Look for solutions with demonstrated success in comparable Indian environments. Choose tools that align with your risk profile and budget.
The following table summarizes key data breach prevention technologies:
To help you choose the right security solution for your business, we’ve put together a comparison table highlighting the strengths and weaknesses of various technologies.
Comparison of Data Breach Prevention Technologies
| Technology | Effectiveness | Implementation Complexity | Cost Range (₹) | Best Suited For |
|---|---|---|---|---|
| Multi-Factor Authentication (MFA) | High | Low | Varies based on solution | All organizations |
| Data Encryption (at rest and in transit) | High | Medium | Varies based on solution | Organizations handling sensitive data |
| Intrusion Detection/Prevention Systems (IDS/IPS) | Medium | High | Varies based on solution | Organizations with complex networks |
| Security Information and Event Management (SIEM) | High | High | High | Large organizations with dedicated security teams |
| Data Loss Prevention (DLP) | High | Medium | Medium to High | Organizations handling confidential information |
This table offers a quick overview of some commonly used technologies to prevent data breaches, considering their effectiveness, complexity, and cost. It’s essential to analyze your organization’s specific needs to determine the best fit.
By carefully selecting and implementing these safeguards, organizations in India can greatly reduce their breach risk and protect valuable assets. This demands a proactive, strategic approach tailored to the unique challenges of the Indian business landscape. Remember, preventing breaches isn’t just about having the newest technology, but about using it effectively and adapting it to your specific situation.
The Human Element: Transforming Staff Into Security Assets

Your employees can be your greatest strength when it comes to data security, or they can be your biggest weakness. This isn’t just about firewalls and antivirus software; it’s about fostering a culture of security awareness. Leading Indian organizations are recognizing this and building security-conscious cultures that strengthen their human security perimeter without disrupting established workplace practices.
Cultivating a Security-First Culture
True security isn’t about strict rules and punishments. It’s about creating a workplace where everyone understands the importance of data protection and feels empowered to take part. Encourage open communication. For example, employees should feel comfortable reporting suspicious emails or activities without fear of being reprimanded. This proactive approach, where everyone contributes, builds a much stronger defense. You might be interested in learning more about best practices for Human Resources in India.
Tailoring Training to the Indian Workforce
Generic security awareness training often misses the mark. Effective training must resonate with the diverse Indian workforce, considering different generations, job roles, and educational backgrounds. Using relatable examples and offering training in local languages can significantly improve comprehension and engagement. Remember, a sales representative faces different security challenges than a software developer. Role-specific training is key.
Beyond Completion Rates: Measuring True Awareness
Simply tracking how many employees complete a training course doesn’t tell the whole story. Are they actually retaining the information and putting it into practice? More engaging methods, like simulated phishing attacks or quizzes, can help you gauge true awareness. These tools help identify areas where employees might need more support, allowing you to refine your training programs for maximum impact. For more advanced technical safeguards, explore how to Protect Your AI Model From Attackers.
Empowering Security Champions
Consider establishing a network of security champions within each department. These individuals can serve as go-to resources for security questions and promote best practices within their teams. They act as a bridge between the dedicated security team and other departments, fostering a more collaborative and integrated approach to data protection. This distributed model significantly strengthens the overall security posture of your organization.
Building a Culture of Responsibility
Data security shouldn’t be a chore. Integrate it seamlessly into daily workflows so it becomes second nature. Provide clear, easy-to-follow guidelines on data handling, password management, and device security. When security practices are accessible and straightforward, they become less of a burden and more of a natural part of the workday. This ultimately enhances productivity and reduces the risk of breaches. A security-conscious workforce is a powerful asset. By focusing on the human element, you can transform your staff into a robust first line of defense.
Regulatory Navigation: Compliance as a Prevention Strategy
India’s evolving regulatory landscape presents both challenges and opportunities for organizations serious about preventing data breaches. This section offers a practical guide to navigating key regulations, transforming compliance requirements into strategic security advantages.
The Digital Personal Data Protection Act 2023: A Cornerstone of Data Security
The Digital Personal Data Protection Act 2023 (DPPA) is a landmark piece of legislation in India’s data protection journey. This Act establishes a comprehensive framework for the collection, processing, and storage of personal data. Understanding the DPPA’s requirements is essential for any organization operating in India. The act sets strict guidelines for obtaining consent, guaranteeing data security, and establishing accountability for data breaches. It provides a solid foundation for data security, aligning Indian regulations with global data protection standards.
Turning Compliance Into a Competitive Advantage
Progressive companies see compliance not as a burden, but as a chance to improve their security posture. By integrating compliance requirements into their security strategy, these organizations build robust security frameworks that minimize breach risks. For instance, implementing the data minimization principle required by the DPPA not only ensures compliance, but also limits the potential impact of a data breach. This involves collecting and storing only the data absolutely necessary for business operations.
Navigating Upcoming Regulatory Shifts
India’s regulatory landscape is constantly changing. Staying informed about proposed changes and anticipating their impact is vital for maintaining a proactive security strategy. By understanding future regulatory trends, organizations can adapt their security frameworks in advance and avoid expensive last-minute adjustments. This forward-thinking approach ensures continuous compliance and strengthens resilience against emerging threats. You might be interested in: How to master compliance.
Consequences of Non-Compliance
The repercussions of non-compliance with data protection regulations in India can be serious. The DPPA outlines penalties for violations, including hefty fines and potential legal action. These penalties can significantly affect an organization’s financial stability. Moreover, non-compliance can tarnish an organization’s reputation and diminish customer trust. This reputational damage can have lasting effects on business growth and sustainability.
Building a Resilient Governance Structure
Building a strong governance structure is essential for adapting to evolving regulatory requirements. This involves establishing clear roles and responsibilities for data protection, implementing effective data governance policies, and conducting regular security audits. A resilient governance structure allows organizations to respond quickly to regulatory changes and ensures continued compliance. This proactive approach bolsters the organization’s overall security posture and builds trust with stakeholders.
Practical Approaches for Compliance
Implementing effective compliance practices requires a practical, step-by-step approach:
- Conduct a data inventory: Identify all personal data collected, processed, and stored by your organization.
- Implement data protection policies: Develop comprehensive policies outlining data handling procedures, access controls, and security measures.
- Provide employee training: Educate your staff on data protection best practices and compliance requirements.
- Conduct regular audits: Assess your security posture and compliance status through regular security audits and penetration testing.
- Establish an incident response plan: Develop a clear incident response plan to manage data breaches efficiently and minimize their impact.
By implementing these practical steps, organizations can successfully navigate India’s regulatory landscape, fortify their security posture, and build a resilient framework for preventing data breaches.
Measuring What Matters: Security Metrics That Drive Results
Stop guessing about the effectiveness of your breach prevention strategies. This section offers practical frameworks for measuring security performance, specifically within the Indian business context. We’ll explore the metrics that genuinely indicate a lower breach risk and provide actionable advice for both technical teams and business leaders.
Key Metrics for Effective Breach Prevention
The success of your security measures shouldn’t be a mystery. Tracking the right metrics is essential to understand your strengths and vulnerabilities. These metrics should offer a clear view of your security posture and pinpoint areas for improvement. This goes beyond simple compliance checklists, allowing you to demonstrate a tangible return on your security investments.
- Mean Time to Identify (MTTI): This metric tracks how quickly you detect a potential security incident. A lower MTTI is critical for minimizing the damage a breach can inflict.
- Mean Time to Contain (MTTC): MTTC measures how long it takes to control a security incident after detection. A swift MTTC proves your ability to quickly limit a breach’s impact.
- Number of Successful Phishing Attacks: Considering the prevalence of phishing in India, monitoring this metric offers valuable insights into the effectiveness of your security awareness training and email security solutions.
- Vulnerability Remediation Rate: This measures how efficiently your team addresses known vulnerabilities. A high remediation rate showcases a proactive security approach.
- Employee Security Awareness Training Completion and Assessment Scores: Assessing both participation and comprehension is vital for evaluating the success of your training programs.
Building Informative Security Dashboards
Communicating security status effectively relies on clear, concise dashboards. These dashboards should present key metrics in an easy-to-understand way, enabling executives to quickly grasp the current security landscape and make data-driven decisions about resource allocation. A well-designed dashboard can also showcase the value of security investments by highlighting their risk reduction impact.
Demonstrating ROI on Security Investments
Justifying security spending requires demonstrating its value. By tracking metrics like decreased incident response costs and avoided regulatory fines, you can show a tangible return on investment. This strengthens the argument for future security initiatives and ensures ongoing executive buy-in.
Identifying Control Gaps Before Incidents Occur
Metrics can reveal weaknesses in your defenses before a breach happens. For instance, a consistently high MTTI might suggest a need for improved threat detection tools like Splunk. A low vulnerability remediation rate could indicate a lack of security personnel or a need for automated patching solutions. Actively monitoring these metrics enables proactive identification and remediation of security gaps.
Balancing Leading and Lagging Indicators
Effective security measurement uses both leading indicators (predictive metrics like vulnerability remediation rate) and lagging indicators (outcome metrics like the number of breaches). This balanced approach provides a complete picture of your security performance. Leading indicators help predict potential problems, while lagging indicators assess the overall effectiveness of your strategies. This data-driven approach allows for proactive adjustments, moving beyond reactive security measures to establish a truly resilient defense. This is a key step in continuously improving your security posture.
To learn more about strengthening your background check processes and minimizing insider threats, visit SpringVerify for comprehensive background verification services designed for the Indian market.






